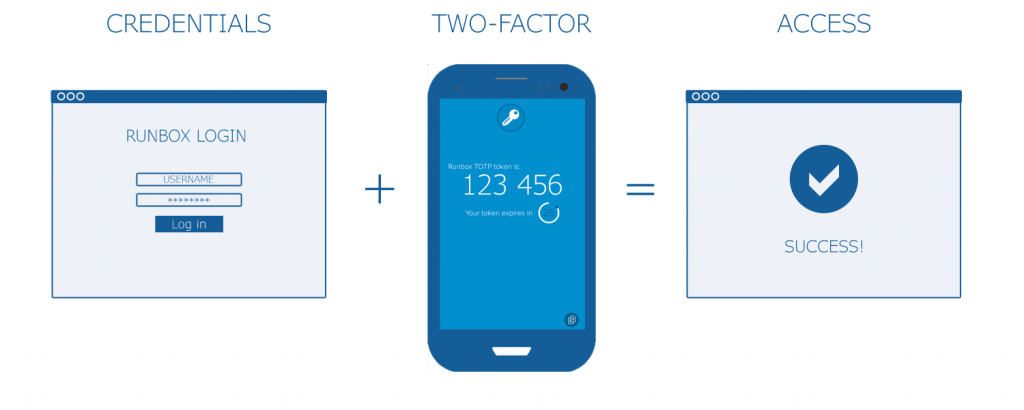
Runbox recently launched Two-Factor Authentication (2FA). 2FA is a log in procedure where an additional piece of information is required in addition to your username and account password.
This additional factor is a code that can only be used once, or for a limited period of time.
Runbox 2FA currently supports Timed One-Time Passwords (TOTP) and One-Time Passwords (OTP) as additional factors. We are planning to expand this with Yubikey or U2F support.
Runbox is the only 2FA-enabled email provider in Norway
 Runbox is located in Norway, which has some of the strongest privacy regulations in the world.
Runbox is located in Norway, which has some of the strongest privacy regulations in the world.
By choosing Runbox as your email provider, your data will be protected by these regulations while ensuring your email is secure from unauthorized access.
Read on to find out how Runbox 2FA works and which options are available.
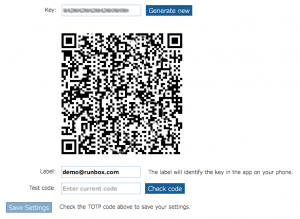
Timed One-Time Passwords (TOTP)
To use this option you will need a smartphone and some free software.
Timed one-time passwords works by giving you a login code which changes over time, in addition to your password.
To get started, download a TOTP app such as Authy, FreeOTP or Google Authenticator onto your mobile phone and follow their instructions.
Note: It is essential that your smartphone has the correct date/time set as this is used by the TOTP app to generate the correct codes that allow you to log in.
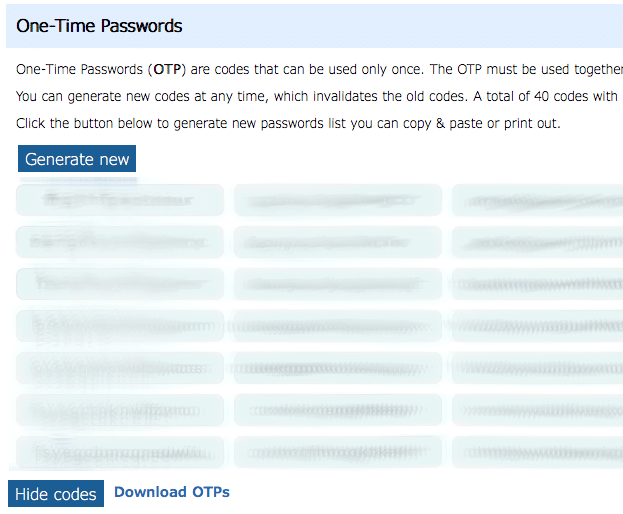
One-Time Passwords (OTP)
When you enable this option, the system will generate random passwords that you can use only once. Used passwords are discarded automatically and cannot be used again.
You can download the the list of passwords to a computer or mobile device, or you can print them out if necessary. However, you must keep the list secure as these passwords can be used to access your account along with your usual username and account password.
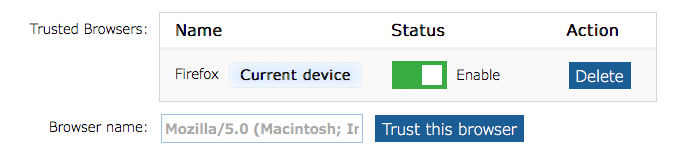
Trusted browsers
This option allows the server to trust your current web browser so that you don’t have to use a 2FA code. The option places a small piece of code in your browser (a cookie) that tells the server not to require the 2FA details and you can just log in with username and password.
You should only use this method of bypassing 2FA on a computer or device that you are confident nobody else can log in to. You can temporarily turn on/off individual browsers from the trusted list, or you can delete the browser entry entirely which will force that browser to require the 2FA details.
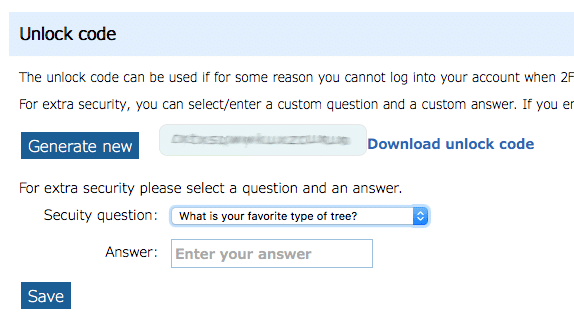
Unlock code
If for some reason you are unable to log in with 2FA after it has been enabled, this code can be used to disable 2FA.
The code can be used in conjunction with a secure question/answer for additional security.

Do you plan to support for hardware FIDO U2F tokens like Yubikey?
Yes, that is the plan, but no timeline yet.
If runbox had support for U2F, I would sign up today.
Any update on the FIDO / yubikey support?
Any Update on the U2F support?
No update, but U2F is important to us, so we will get it.
Please add support for YubiKey. I want to move from another provider but this is the one thing holding me back.
Love to see U2F FIDO FIDO2 support for yubikey/nitrokey/solo. 2FA is too annoying to use and not as secure,
Runbox is listed as Yubikey-supported app at https://www.yubico.com/works-with-yubikey/catalog/. So I guess it already is possible to use Yubikey as 2nd factor, no?
Runbox currently does not support Yubikey, but we are planning to develop support for Yubikey and U2F.
Any update here?
This is still planned but no time frame as of yet.